Articulating risk and framing the potential impact of cyber threats to c-suite executives has become one of the most important roles required to effectively lay the foundation of an organization’s long-term cybersecurity. With the ever-increasing scope of cyber-attacks dominating the headlines, driving corporate wright offs and shuttering 60% of affected SMB within a year, the need to accurately convey the perils of cyber threats to c-suite executives and board members has never been more urgent.
In a world where the news cycle rather than the board is better equipped to understand what is at stake in a data breach, the paradigm must be shifted to where the c-suite can evaluate cyber risk and determine when their organization has been compromised.
While contextualizing cyber risk may not be sexy, driven by the right CISO it can dramatically alter the strategic thinking of critical executive players, breed a legitime sense of urgency and dispel the flawed logic that hackers will always find a way to compromise data, regardless of the consorted efforts of a dedicated few.
Why has there been a disconnect in prioritizing cyber risk?
Francesca Cassidy, in a 2018 Raconteur article astutely remarks that “The frustrating truth for those who care passionately about the benefits of risk management is that the subject remains a turn-off for too many board members and other senior executives. While the profile of risk management is probably higher than ever, it still has negative connotations.”
Fighting negative connotations is dependent on the ability of CISO’s to frame cyber risk management in terms the board can tangibly quantify, removing the stigma and jargon to coalesce on what is at stake.
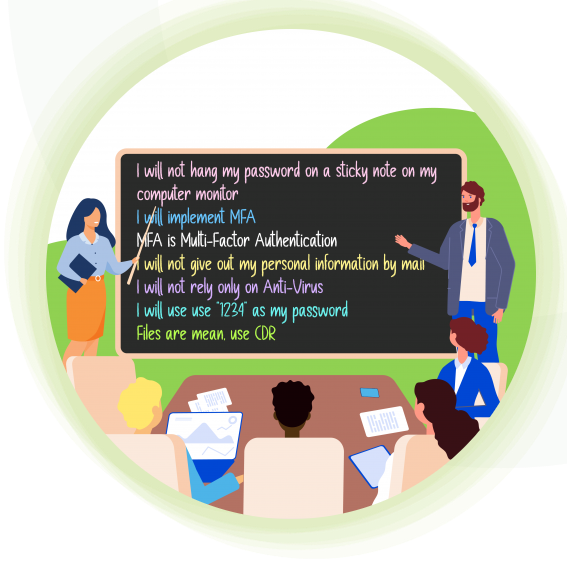
In practice, many CISO fails to effectively convey the clear relationship between technical integration, employee education, and changes in organizational cyber policy, as a result, many c-suite executives lack a true understanding of basic steps, systems, and rationale for decreasing the attack surface and creating a secure and protected environment.
Key Stats
According to recent surveys by PwC and the Harvard Business Review as well as the IBM Institute for Business Value there is a growing trend towards improving cyber resilience across enterprise businesses:
- 48% of c-suites surveyed said building an organization wider cybersecurity culture should be a top priority of CISOs, this increases to 63% when projected over the next 3 years
- 84% of c-suites surveyed said they consider the ability to educate and collaborate across the business to be critical for CISOs
- 66% of C-suite’s views cybersecurity as a top concern that must be addressed
- 55% of c-suites surveyed said to say a CISO should provide periodic threat and incident reports to the board
- 37% of CISO provide an annual cybersecurity strategy and evaluation report
How can we better communicate with the c-suite?
Scale back the technical information
According to Mollie Chard, Cybersecurity Manager at Capgemini:
“Risk as a subject isn’t a turn-off for board members if it’s communicated properly. All too often, I see cybersecurity professionals who can’t take complex technical information and translate it… they swamp the board with technical information, rather than the business information that leadership needs to know. Awareness of the importance of cybersecurity is growing throughout businesses, but there is still an onus on cybersecurity management being able to communicate the subject matter effectively to different stakeholders.”
Explain the metrics of cyber risk
According to Denise Louie, Director of Enterprise Risk & Information Governance at the J.M. Smucker Company:
If you want to speak the language of c-suites you must have the ability to address how cyber threats will alter the “ability to make and deliver the product; future revenue to be generated from trade secrets, intellectual property or other critical data; customer/employee/public trust; market share; and in ally reputation. CISO’s must explain in simple terms the ways cyber risk can materialize, the scale of the IT ecosystem, and the entity’s ability to prevent or minimize even the simplest of cyber events.”
Build a rapport between the CISO and the executive team
If the CISO is viewed as an outsider, they will never be able to truly convey the importance of protecting against cyber threats. In the wake of SolarWinds, the seemingly never-ending attacks on Microsoft Exchange Online, and countless other public shows of force this may be easier to achieve than ever before.
According to the Harvard Business Review: “Leading organizations now understand that the CISO role must shift from a mostly technical role to one centered on providing leadership and partnership across the business—connecting to business and transformation strategies and driving initiatives and solutions that enable the organization to realize its goals.”
How to make cybersecurity a priority?
In generations past, the segmentation of responsibilities and insulation of industries created a mindset that individual risk could be addressed by one professional or dept with occasional assistance from trusted advisors. Today, everything is connected, and this is especially true regarding IT and cyber risk.
As ‘Securing the C-Suite: Cybersecurity perspectives from the boardroom and C-suite succinctly put it: “Cybersecurity issues are no longer limited to the IT department; instead, they threaten every aspect of the organization and pose a significant threat to ongoing business continuity and reputation. They extend well beyond the technical environment and reach across the entire business ecosystem.”
Thank you to Odix for sharing their content.
After years of working in a high-security organization specializing in infrastructure protection, encryption, network security and mobile devices the founders of odix developed a more effective and cost-efficient approach to network security.
odix solution is specifically focused on providing comprehensive network protection by preventing malware attacks – without the massive investment in detection and remediation associated with existing technology.